Why I Started Paying Attention to Mythos
When I first heard about Anthropic’s Mythos during a casual chat with a colleague from the IT consulting space, I thought it was just another AI tool that would help us spot bugs faster. But the more I read especially the breaking news about it being able to chain together multiple vulnerabilities the more I felt a chill. It’s not every day that a piece of software can act like a hacker, automatically looking for hidden gaps and even simulating an attack. This caught people’s attention across the industry, and suddenly Mythos became a trending news India story.
In my experience, most AI‑driven security solutions act like a pair of binoculars they help us see threats that are already out there. Mythos, however, is more like a spotlight that can illuminate weaknesses before anyone even knows they exist. That shift from defensive to potentially offensive use is what makes the whole discussion so interesting and a little scary.
What Mythos Actually Does
Picture this: you have a massive codebase, maybe the kind of system that runs the backend of a popular Indian e‑commerce platform. Traditionally, a team of security engineers would spend weeks, sometimes months, manually combing through the code, looking for patterns that could be exploited. Mythos changes the game. It scans the entire software ecosystem, identifies hidden vulnerabilities, and then automatically pieces together how those flaws could be combined for a multi‑step attack.
In plain terms, it’s like having a virtual hacker that never gets tired. It can find a memory leak, link it to an authentication bypass, and then suggest a way to exfiltrate data all in a matter of hours. The model works autonomously, meaning it doesn’t need a human to tell it what to look for; it decides based on its own analysis. This autonomy is what many experts, including Maaz Ansari, CRO & Co‑founder of Oriserve, refer to as a "qualitative leap" in AI capabilities.
How I See the Alarm Bells Ringing
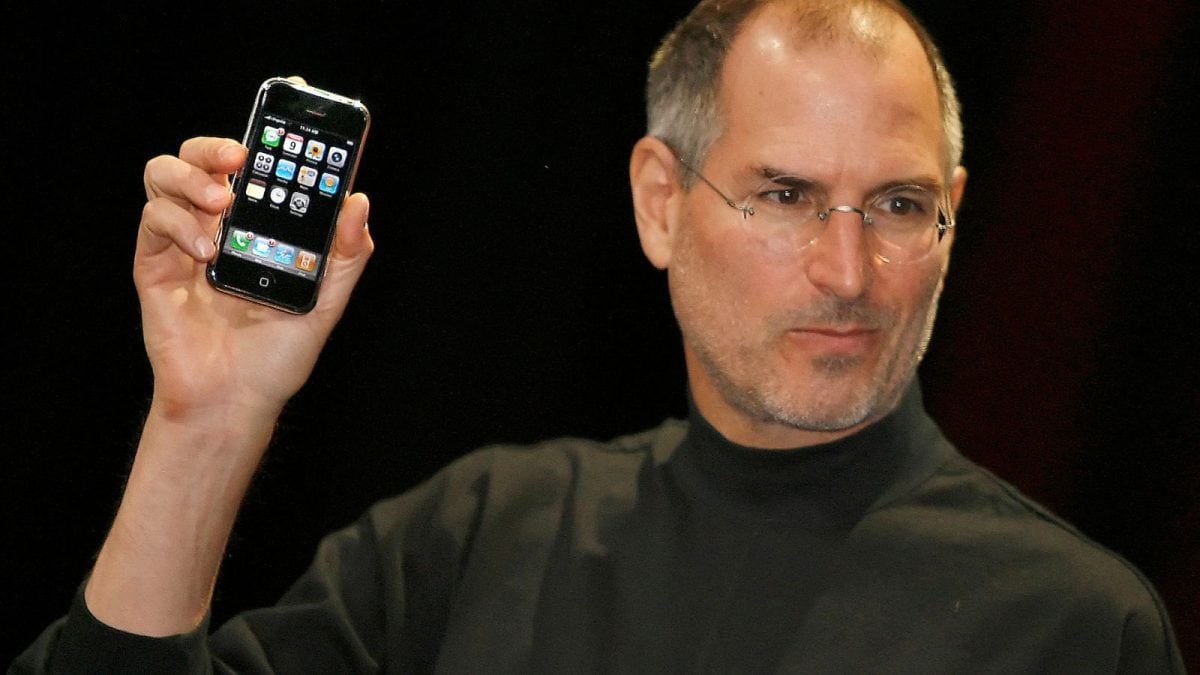
Anthropic isn’t rolling out Mythos to the public just yet. They’ve limited access to a select group of big players Amazon, Apple, JP Morgan Chase, Cisco and Nvidia through a programme they call Project Glasswing. The idea is to let these organisations tighten their own defenses before a similar AI tool becomes a part of the wider market.
But think about it: if a tool that can automatically discover and exploit vulnerabilities becomes as easy to use as a smartphone app, the barrier to entry for cyber‑attacks drops dramatically. In my view, it’s like moving from professional-grade lock‑picking tools to a cheap, mass‑produced kit that anyone can buy. Kanishk Agrawal, CTO of Judge Group India, warned that Anthropic is being "super careful" because the model is "really good at finding weaknesses in software". If the wrong hands get hold of it, the damage could be massive.
AI‑Driven Cyber Warfare The Numbers Behind the Fear
According to a recent SoSafe report that surveyed 500 global security professionals, a staggering 87% of organisations worldwide have already faced an AI‑driven cyberattack. Even more eye‑opening, 91% of those experts expect AI‑powered threats to surge in the next few years. This isn’t just a niche concern; it’s the kind of breaking news that makes headlines in India updates sections of major portals.
What’s happening now is a feedback loop: as offensive AI tools become more advanced, defenders scramble to build AI that can predict, detect and neutralise those attacks in real time. This creates an arms race where machines are both the attacker and the defender. The speed at which these models learn is unlike anything we’ve seen in traditional cyber‑warfare weeks of research can turn into days or even hours of actionable intelligence.
Why Mythos Could Accelerate the Arms Race
Maaz Ansari puts it bluntly: "The real concern is the gap between when attackers figure this out and when defenders are ready." He believes Mythos itself may not be misused per se, but it signals what is now possible. Other AI models will soon catch up, and once they do, the market could be flooded with tools that make hacking as simple as clicking a button.
From my perspective, the problem is two‑fold. First, the discovery of hidden flaws is now almost instantaneous. Second, patching those flaws updating software, testing compatibility, rolling out fixes still takes time. This creates a growing imbalance where the clock is always ticking against defenders. As a result, many organisations may find themselves constantly reacting rather than proactively securing their systems.
What the Experts Say About the Dual‑Use Nature of Mythos
Venkat Lakshminarasimha, Executive Director & Head of Solutions (India & Middle East) at Dexian, argues that despite its flaws, Mythos is still a valuable ally. He says the model can help companies spot problems before they become real attacks, predict when a breach might happen, and stay one step ahead of cyber‑threats. In my conversations with him, he repeatedly stressed that the tool’s ability to "review millions of lines of code overnight" is something security teams badly need, especially when the talent pool of security engineers is thin.
However, this dual‑use nature makes decision‑making tricky. Too tight a restriction could slow down defensive innovation, but too loose an access could hand powerful weapons to the wrong actors. As I see it, the balance lies in controlled collaboration letting trustworthy partners test the model, learn from it, and then share defensive techniques with the wider community.
Geopolitics and the New AI‑Powered Battlefield
Beyond corporate boardrooms, Mythos is already becoming a topic in the realm of geopolitics. Kanishk Agrawal notes that advanced AI models are now treated as strategic assets, much like ballistic missiles or nuclear technology. Nations are beginning to see AI capabilities as a measure of both economic productivity and military advantage. In an age where cyber‑espionage can cripple critical infrastructure, governments are likely to impose export controls and forge alliances around AI technology.
From my observation of the latest trends, this could reshape international relations. Countries that master frontier AI models like Mythos may gain an edge not just in tech markets but also in diplomatic negotiations. It’s a scenario where "cyber‑security" is no longer a purely technical term but a component of national security strategy.
The Road Ahead What Should We Expect?
Looking forward, I think we’re heading into a world where pure human‑only security teams become a myth. Maaz Ansari summed it up nicely: "You cannot defend against AI‑speed attacks with human‑speed response." Companies that embed AI into their security operations today will likely stay ahead; those that wait may find themselves overwhelmed.
But it’s not all doom and gloom. The same technology that can uncover hidden bugs can also suggest patches, highlight exploitable paths, and even simulate attacks to test defenses. The critical question is who gets to use these tools first. If the "good guys" adopt them early, the balance could tilt in favour of defenders. If not, we might see a surge in AI‑driven cyber‑crime that spreads like a viral news story across the internet.
In conclusion, Mythos is a clear illustration of how AI is moving from being a supportive assistant to a potential adversary. It forces us to rethink security policies, industry collaborations, and even national strategies. As a tech enthusiast who follows the latest news India widely, I’ll be keeping a close eye on how this story unfolds, because the ripple effects will be felt across every sector from banking to e‑commerce, from government services to the everyday smartphone user.
Final Thoughts
To wrap things up, think of Mythos as a double‑edged sword. It can shave weeks off the time it takes to find a critical flaw, but it can also hand that same knowledge to anyone with malicious intent. The challenge for us whether we are security professionals, policymakers, or just regular internet users is to ensure the right safeguards are in place while still leveraging the benefits.
Stay tuned, because the conversation around AI in cyber‑security is only getting louder, and you’ll likely see more stories like this popping up in viral news feeds and trending news India sections in the days to come.